Stage2: Difference between revisions
| Line 130: | Line 130: | ||
|} | |} | ||
The 3DS TWL_FIRM verifies TWL RSA padding with the following | The 3DS TWL_FIRM verifies all TWL RSA padding with the following. It's unknown whether the DSi Stage1 has the same code as TWL_FIRM for this, the RSA padding data(not the actual hashdata) contained in the DSi bootloader signature and TWL_FIRM bootloader are the same at least. This is different from how the main DSi "BIOS" RSA padding check code does it as well. | ||
* The first byte must be 0x0. | * The first byte must be 0x0. | ||
* The second byte must be 0x1 or 0x2. | * The second byte must be 0x1 or 0x2. | ||
* Executes a while(<value of byte at current pos in RSA message>). When the second_byte in the message is 0x1, the byte at curpos must be 0xFF(otherwise the non-zero value of the byte at curpos doesn't matter). This loop must find a zero byte before offset 0x7F in the message otherwise an error is returned. | * Executes a while(<value of byte at current pos in RSA message>). When the second_byte in the message is 0x1, the byte at curpos must be 0xFF(otherwise the non-zero value of the byte at curpos doesn't matter). This loop must find a zero byte before offset 0x7F in the message otherwise an error is returned. | ||
* Returns an address for msg_curpos+1. | * Returns an address for msg_curpos+1. | ||
With the code in 3DS TWL_FIRM, the actual "totalhashdatasize" in the RSA message must be <=0x74. The 3DS TWL_FIRM code copies the RSA "hashdata" to the output buffer, using the actual size of the RSA "hashdata". | With the code in 3DS TWL_FIRM, the actual "totalhashdatasize" in the RSA message must be <= <expected hashdata_size>(0x74 for bootloader). The 3DS TWL_FIRM code copies the RSA "hashdata" to the output buffer, using the actual size of the RSA "hashdata". | ||
Note that this sector (and two similar ones at 0x400 and 0x600) appear to be the only unencrypted blocks on the NAND flash. | Note that this sector (and two similar ones at 0x400 and 0x600) appear to be the only unencrypted blocks on the NAND flash. | ||
Revision as of 08:04, 9 March 2015
Stage 1
The first stage of the DSi's bootloader lives in ROM, presumably on the CPU die. It loads further encrypted+signed stages from NAND flash, starting with a plaintext offset table in the sector at offset 0x200.
Not much is known about this bootloader yet, but it presumably knows how to:
- Initialize the encryption hardware
- Read the contents of NVRAM
- Initialize both LCDs
- Read blocks (but not files) from the NAND flash
- Perform some variety of integrity check on all data it reads (signature, CRC, ?)
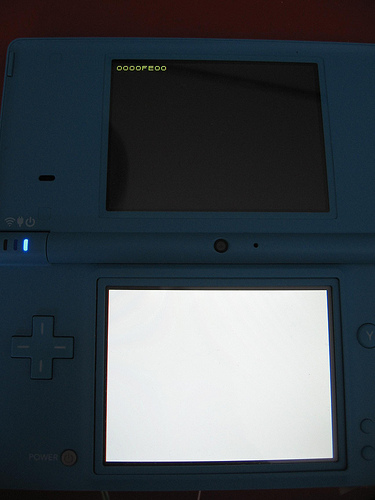
- Display basic hexadecimal error codes
- Possibly factory-programming the NAND flash?
- Might also do basic power-on self test of peripherals
Known error codes:
| Error Code | Description |
|---|---|
| 0000FE00 | Error communicating with NAND chip. (It's missing, CLK is shorted, etc.) |
| 0000FEFC | Integrity error in first block of Stage 2 (address at 0x220) |
| 0000FEFD | Integrity error in second block of Stage 2 (address at 0x230) |
| 0000FEFE | Boot sector integrity error (Sector 0x200 not valid), or error in NVRAM contents. |
Stage 2

Unlike the stage1 bootloader, which must be small enough to fit in ROM (probably several kilobytes), the stage2 bootloader has about a megabyte of NAND flash reserved for it. The stage2 bootloader understands partitions and filesystems, and it is capable of loading the DSi menu. It also must understand the encryption used on filesystem blocks in the NAND, and it must understand how to load and validate title metadata.
The Stage 2 loader was not modified by the System Menu 1.4 update. This is still earlier in the boot process than the "Health and Safety" warning(that warning is displayed by the sysmenu).
The first stage bootloader reads the sector at offset 0x200 in order to find a table of offsets to the Stage 2 bootloader:
00000220 00 08 00 00 10 64 02 00 00 80 7b 03 00 66 02 00 |.....d....{..f..|
00000230 00 6e 02 00 88 75 02 00 00 80 7b 03 00 76 02 00 |.n...u....{..v..|
00000240 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 |................|
This is describing two chunks of the stage2 loader: the ARM9-binary 0x26410 bytes in length at address 0x800, and the ARM7-binary 0x27588 bytes at address 0x26e00.
Structure of this header:
| Offset | Size | Description |
|---|---|---|
| 0x0 | 0x20 | Reserved |
| 0x20 | 0x10*2 | Two binary-block headers: first one is for the ARM9 binary, second one for the ARM7 binary. |
| 0x40 | 0xBF | Reserved |
| 0xFF | 0x1 | Unknown, value 0xFF. |
| 0x100 | 0x80 | RSA-1024 signature |
| 0x180 | 0x80 | Unknown |
Structure of the binary-block headers:
| Offset | Size | Description |
|---|---|---|
| 0x0 | 0x4 | Offset for this binary in NAND. |
| 0x4 | 0x4 | Actual binary size. |
| 0x8 | 0x4 | Binary load address in memory. This is also the binary entrypoint. |
| 0xC | 0x4 | Binary size aligned to 0x200-bytes. |
Structure of the 0x74-byte "hash-data" stored in the RSA message:
| Offset | Size | Description |
|---|---|---|
| 0x0 | 0x10 | AES_Engine keyY used for the ARM9/ARM7 binaries crypto. |
| 0x10 | 0x14 | SHA1 hash. Going by 3DS TWL_FIRM this seems to calculated over the first 0x28-bytes of NAND, then the first 0x100-bytes of the header, then the last 0x80-bytes of the header(following the signature). This works with the bootloader contained in TWL_FIRM, however it's unknown how the first part is handled on DSi. |
| 0x24 | 0x14 | SHA1 hash over the plaintext ARM9 binary, with the actual binary size. |
| 0x38 | 0x14 | SHA1 hash over the plaintext ARM7 binary, with the actual binary size. |
| 0x4C | 0x14 | Unknown, not used by 3DS TWL_FIRM. Normally all-zero. |
| 0x60 | 0x14 | Unknown, not used by 3DS TWL_FIRM. |
The 3DS TWL_FIRM verifies all TWL RSA padding with the following. It's unknown whether the DSi Stage1 has the same code as TWL_FIRM for this, the RSA padding data(not the actual hashdata) contained in the DSi bootloader signature and TWL_FIRM bootloader are the same at least. This is different from how the main DSi "BIOS" RSA padding check code does it as well.
- The first byte must be 0x0.
- The second byte must be 0x1 or 0x2.
- Executes a while(<value of byte at current pos in RSA message>). When the second_byte in the message is 0x1, the byte at curpos must be 0xFF(otherwise the non-zero value of the byte at curpos doesn't matter). This loop must find a zero byte before offset 0x7F in the message otherwise an error is returned.
- Returns an address for msg_curpos+1.
With the code in 3DS TWL_FIRM, the actual "totalhashdatasize" in the RSA message must be <= <expected hashdata_size>(0x74 for bootloader). The 3DS TWL_FIRM code copies the RSA "hashdata" to the output buffer, using the actual size of the RSA "hashdata".
Note that this sector (and two similar ones at 0x400 and 0x600) appear to be the only unencrypted blocks on the NAND flash.
After loading+verifying the the above header, the ARM7 binary is loaded+verified, then the ARM9 binary is loaded+verified.
Whereas the filesystem data in NAND is encrypted using a unique key for every DSi, the stage2 bootloader is identical on every DSi tested so far. The stage2 bootloader binaries are not encrypted with any console-unique keys.
Stage1 uses the AES_Engine to decrypt each ARM9/ARM7 binary, where keyY is from the above signature. The AES_Engine keyslot used here is the same one used for the shared areas for Tad, therefore the keyX is the same as the one used for that. The following is used for the CTR, where "binblk->binblocksize" is the actual binary size:
unsigned int ctr[4]; memset(ctr, 0, 16); ctr[0] = binblk->binblocksize; ctr[1] = (unsigned int)(-binblksize); ctr[2] = ~binblk->binblocksize;
Stage2 operations
After Stage 2 is loaded:
- The NAND flash is partially re-initialized
- Sector 0 is read from the NAND. This appears to be an (encrypted) DOS-style MBR.
- The MBR signature and the type of the first partition are verified.
- Filesystem metadata is read from sectors starting around 0x100000. The metadata appears to be in FAT32 format with long filenames.
- Multiple files are loaded from the filesystem. The exact read addresses will vary depending on your DSi's firmware version and the state of its filesystem when you performed the last firmware update. On a brand new DSi, it appears that the DSi Menu itself is loaded from 0xb20000 after two small metadata files are read from 0xb1c000 and 0x7a0000.
All errors show before the health and safety screen. It appears that stage2 errors from a cold power-on always cause the DSi to hang at a black screen, whereas stage2 errors after reset (pressing but not holding the power button) will give an error message screen. Known errors:
| Text | Description |
|---|---|
| "Error: 1-2435-8325" | Invalid signature or partition type in MBR, invalid starting LBA. |
| "Error: 3-2435-8325" | DSi Menu integrity checks failed |